Written by:
Editorial Team
Editorial Team
Data security compliance is the process of managing data according to laws, industry rules, and internal policies. It is a strategic framework for protecting sensitive information—from customer lists to intellectual property—from unauthorized access, use, or disclosure. Effective compliance combines technical safeguards, organizational policies, and continuous monitoring.
Why Data Security Compliance Is a Strategic Imperative

As a Chief Information Security Officer (CISO), your primary challenge is no longer just defending against external threats. It involves navigating a complex patchwork of global data protection laws, such as Europe's GDPR and California's CCPA, without hindering business innovation. The financial and reputational risks are significant; fines for non-compliance can reach billions of dollars.
This guide explains how to approach data security compliance as a strategic advantage rather than a checklist. A strong compliance program builds customer trust and can open new markets. The core problem this article addresses is how to create a scalable compliance framework that avoids fines and supports the safe adoption of new technologies like AI.
Moving Beyond a Reactive Stance
For years, many companies treated compliance as a reactive, annual task focused solely on passing an audit. This approach is no longer viable.
A modern compliance strategy must be proactive and continuous. It requires embedding security and privacy principles into all organizational processes, from product development to data disposal.
This shift is critical. Understanding the importance of data security compliance means recognizing the need to protect your company from data breaches at every point in the data lifecycle. A proactive program delivers benefits beyond penalty avoidance.
- Enhanced Customer Trust: Demonstrating a commitment to data protection builds consumer confidence. According to a 2023 consumer survey by a major consulting firm, 76% of consumers stated they would stop doing business with a company after a data breach.
- Improved Operational Efficiency: A well-defined compliance framework standardizes processes, clarifies responsibilities, and reduces the friction caused by ad-hoc security fixes.
- Accelerated Innovation: Clear guidelines on data usage empower teams to experiment with new technologies, such as AI and machine learning, in a responsible manner.
This article outlines a path from foundational concepts to actionable frameworks, highlighting the role of automation in achieving sustainable compliance.
Understanding Core Regulations and Frameworks
Navigating data security compliance involves understanding two key components: regulations and frameworks. Regulations are legally binding rules that an organization must follow. Frameworks are structured collections of best practices that provide a blueprint for building a secure organization.
A robust compliance strategy integrates both. Regulations define the legal requirements to avoid penalties, while frameworks offer efficient methods for implementation. Ignoring regulations leads to fines and legal action. Ignoring frameworks results in a disorganized and insecure program. For example, using the framework from the National Institute of Standards and Technology (NIST) can help build a security program that satisfies the requirements of regulations like GDPR.
The Difference Between Regulations and Frameworks
Regulations are mandatory laws enacted by governments. They establish the minimum legal requirements for data protection and carry significant penalties for non-compliance.
Frameworks are typically voluntary sets of guidelines and best practices developed by industry bodies or government agencies. They provide a structured approach to achieving security and meeting legal requirements.
A useful analogy: a regulation is a law stating that all new buildings must be earthquake-proof. A framework is the detailed engineering blueprint showing how to construct the foundation and reinforce the structure to withstand a tremor. One is the rule; the other is the method.
Understanding this distinction is the first step toward building a compliance program that is both legally sound and operationally effective.
Key Global Data Security Regulations at a Glance
The global regulatory landscape is complex. As of early 2025, 144 countries had data protection laws in place, covering 6.3 billion people, or 79% of the global population.
The financial investment is also substantial. A 2024 survey showed that 27% of large organizations spend over $500,000 annually on GDPR compliance alone. You can learn more about how data privacy statistics impact global business on usercentrics.com.
Here is a brief overview of some critical regulations.
| Regulation | Geographical Scope | Core Requirements | Maximum Penalties |
|---|---|---|---|
| GDPR | European Union (EU) & European Economic Area (EEA), plus any entity processing EU residents' data. | Consent, data minimization, right to be forgotten, data breach notification within 72 hours, data protection officers (DPOs). | Up to €20 million or 4% of annual global turnover, whichever is higher. |
| CCPA / CPRA | California, USA. Applies to businesses that meet specific revenue or data processing thresholds. | Right to know, right to delete, right to opt-out of data sale/sharing. CPRA added rights to correct and limit use of sensitive data. | Up to $7,500 per intentional violation and $2,500 per unintentional violation. |
| HIPAA | United States. Applies to healthcare providers, health plans, and their business associates. | Strict privacy and security rules for Protected Health Information (PHI), including administrative, physical, and technical safeguards. | Fines range from $100 to $50,000 per violation, with an annual cap of $1.5 million. Criminal penalties are also possible. |
This table provides a high-level summary. The specific requirements and penalties can vary significantly by region.
Foundational Security Frameworks
While regulations define the destination, frameworks provide the roadmap. Adopting a recognized framework standardizes your approach, simplifies audits, and demonstrates due diligence to regulators and partners.
Two of the most influential frameworks are:
- NIST Cybersecurity Framework (CSF): Developed by the U.S. government, the CSF provides a strategic view of managing cybersecurity risk. It is organized around five functions: Identify, Protect, Detect, Respond, and Recover. Its flexibility makes it a popular choice for organizations of all sizes.
- ISO/IEC 27001: This is the international standard for an information security management system (ISMS). Unlike the CSF, it allows for formal certification. Certification to ISO 27001 is a recognized method for demonstrating a strong security posture. It is more prescriptive and requires a comprehensive risk assessment and the implementation of specific controls.
The choice of framework depends on your industry, operational regions, and business goals. Many organizations use a hybrid model, applying the NIST CSF for overall strategy while implementing specific ISO/IEC 27001 controls for high-risk areas. This approach helps ensure a data security compliance program is both strategically sound and certifiably robust.
Implementing Essential Security Controls
After understanding the applicable regulations and frameworks, the next step is implementation. Security controls are the practical safeguards put in place to protect information. Effective data security compliance requires a layered defense that combines technical and organizational measures.
Technical controls are technology-based defenses built into systems. Organizational controls are the policies and procedures that guide human behavior. These two types of controls must work together to create a strong security posture.
Technical Controls: Your Digital Fortress
Technical controls are the first line of defense against unauthorized access to sensitive information. Implementing them is a core requirement of nearly every major data protection regulation.
Key technical controls include:
- Encryption: This process scrambles data, making it unreadable without a decryption key. It should be applied to data at rest (stored on a server or hard drive) and in transit (moving across a network). For example, if a server with an encrypted customer database is stolen, the data itself is useless to the thief.
- Access Control: Not all employees need access to all data. Role-Based Access Control (RBAC) is a fundamental principle that grants individuals access only to the data required for their job functions. A sales representative needs access to the CRM but should not have access to sensitive R&D or financial records.
- Firewalls and Network Security: These act as gatekeepers for a digital network. They monitor and filter traffic between an internal network and the internet based on a set of security rules.
A common error is to treat these controls as a one-time setup. Compliance requires continuous auditing of configurations, regular penetration testing, and updating defenses to address new threats.
Organizational Controls: Guiding Human Action
Technology alone cannot prevent human error. Organizational controls are essential for managing risks associated with human behavior. These controls help build a security-conscious culture and establish clear processes for handling data.
Key organizational controls include:
- Security Awareness Training: Regular employee training on security best practices is a cost-effective measure. Training should be ongoing and cover topics like identifying phishing emails, using strong passwords, and handling sensitive data. Synthetic example: running simulated phishing campaigns can reduce employee click-through rates on malicious links by up to 75% over a 12-month period.
- Incident Response Planning: A documented plan for responding to a data breach is critical. An incident response plan details the steps for identifying, containing, and eradicating threats, as well as post-incident analysis. Conducting tabletop exercises helps ensure the team can react quickly and effectively to minimize damage.
- Third-Party Risk Management (TPRM): Security is dependent on the security of partners and vendors. TPRM is the process of vetting the security and compliance of every vendor that handles your data. This includes incorporating security requirements into contracts, conducting regular audits, and establishing clear data processing agreements.
Managing Your Supply Chain Risk
Managing third-party risk is crucial. Modern businesses rely on a network of vendors, each representing a potential entry point for attackers. A 2024 industry report found that over 82% of organizations have experienced a business disruption due to a third-party incident, and 57% of data breaches originated from a supply chain vulnerability.
Despite this, only 19% of enterprises report having complete visibility into their data processing chains, a gap that compliance frameworks are increasingly addressing. You can find more compliance statistics about third-party risk management on complianceandrisks.com.
A strong TPRM program is a cornerstone of data security compliance. Our guide on automating Third-Party Risk Management provides information on building a more resilient and compliant supply chain.
Your Four-Step Compliance Roadmap
Achieving data security compliance is a continuous cycle of improvement, not a one-time project. A repeatable, four-step roadmap makes the process manageable and creates a feedback loop for strengthening security over time.
This section outlines such a framework.
Step 1: Assessment and Gap Analysis
The starting point is a thorough assessment of your current policies, technical controls, and processes against the regulations that apply to your business. The goal is to identify gaps between your current state and your required state. A gap analysis produces a prioritized list of vulnerabilities, indicating where to focus remediation efforts.
Key activities include:
- Data Mapping: Identifying what sensitive data you hold, where it is stored, and how it moves through your systems.
- Control Auditing: Verifying that existing security controls, such as encryption and access rules, are functioning as intended.
- Policy Review: Ensuring internal policies and procedures align with legal requirements and industry best practices.
Step 2: Remediation and Implementation
Once gaps are identified, the next step is to close them. This phase involves implementing new controls, updating policies, and reconfiguring systems to meet requirements. The focus should be on addressing the highest-priority risks first to achieve the greatest security impact quickly.
This stage translates assessment findings into measurable improvements. For more details on this process, our guide on preparing for a data security audit offers practical advice.
Step 3: Continuous Monitoring
Compliance is not static. Threats, regulations, and business operations evolve. Continuous monitoring uses automated tools and regular manual checks to identify new risks before they become significant problems.
Effective compliance programs function like a smoke detector, providing early warnings to address small issues before they escalate into crises.
Effective monitoring includes a mix of:
- Automated Scanning: Using tools to continuously check networks and applications for new vulnerabilities.
- Log Analysis: Monitoring system logs to identify unusual activity or policy violations.
- Regular Audits: Conducting periodic internal checks to ensure controls remain effective.
Step 4: Reporting and Documentation
The final step is to document the work performed. Good documentation serves as evidence for auditors, regulators, and customers, demonstrating a serious commitment to data security compliance. It creates a clear, auditable trail of all compliance activities.
This infographic provides an overview of how security controls span people, technology, and partners.
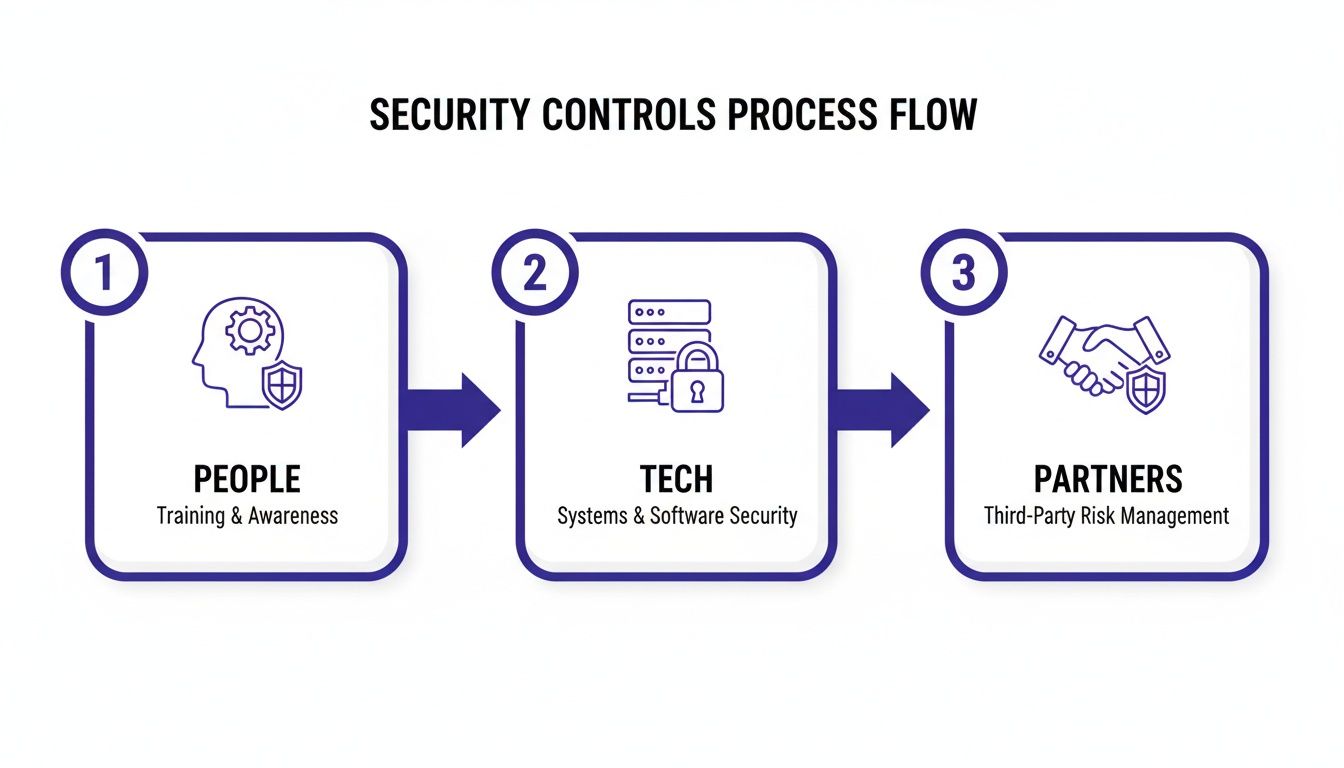
A comprehensive strategy must include human training, secure technology infrastructure, and risk management for all vendors.
Clear reports also provide leadership with the visibility needed to understand the company's risk profile and make informed decisions. The insights from monitoring and reporting feed back into the assessment phase, restarting the cycle.
Navigating Compliance in the Age of AI
Artificial intelligence introduces new challenges to traditional data security compliance. Existing frameworks were not designed for the unique characteristics of machine learning, such as algorithmic bias, model explainability, and the provenance of training data.
For example, an AI model trained on historical hiring data may learn to replicate past biases, leading to discriminatory outcomes and legal risk. If an organization cannot explain why its model denied a loan application, it may violate regulations that require explainability.
A dedicated Responsible AI framework is now essential for managing these new risks throughout the model lifecycle, from development to deployment.
The Rise of AI-Specific Regulations
Regulators are developing new rules to govern AI. The European Union's AI Act is a significant piece of legislation setting a global standard for AI governance. It classifies AI systems based on their level of risk.
The EU AI Act imposes strict requirements on "high-risk" systems, such as those used in critical infrastructure, hiring, or law enforcement. These requirements cover risk management, data governance, transparency, and human oversight. Non-compliance can result in substantial fines.
This regulatory trend indicates that securing the data an AI uses is no longer sufficient. Organizations must also demonstrate that the AI models themselves are fair, transparent, and operate safely. Our guide on achieving EU AI Act readiness provides a detailed breakdown of the requirements.
Key Compliance Risks in AI and Machine Learning
Managing AI requires a shift from protecting data at rest to governing algorithmic behavior. Compliance programs must evolve to address risks specific to machine learning.
Key risks include:
- Algorithmic Bias: Models trained on biased data will produce biased results. A modern compliance framework needs processes to test for and mitigate bias to ensure fair outcomes.
- Lack of Explainability: Many complex models are "black boxes," making it difficult to understand how they arrive at a decision. Regulations are increasingly demanding transparency, requiring organizations to explain model outputs, particularly those with significant impact on individuals.
- Model Drift: An AI model's performance can degrade over time as it encounters new data that differs from its training set. This phenomenon, known as "drift," requires continuous monitoring and periodic retraining to maintain accuracy and fairness.
- Data Provenance: Organizations must be able to demonstrate that their training data was sourced ethically and legally. Using data of questionable origin can introduce bias and lead to compliance violations.
Addressing these AI-specific risks requires specialized tools. According to critical statistics from complianceandrisks.com, top-performing companies are adopting AI with governance integrated from the start. This approach reduces risk and improves ROI by ensuring AI initiatives are both effective and compliant.
How Automation Transforms Compliance Management
Manual compliance management using spreadsheets and email is slow, error-prone, and not scalable. This approach turns data security compliance into a reactive and costly process.
Automation with an integrated Governance, Risk, and Compliance (GRC) platform enables a proactive stance. This transforms compliance from a cost center into a strategic asset that improves security and business agility.
From Manual Drudgery to Automated Efficiency
Automation eliminates repetitive tasks, such as manually gathering evidence for audits. An automated system can collect this information continuously in the background. This allows skilled security and compliance experts to focus on higher-value work, like analyzing risk trends and advising on new projects.
Automation changes compliance from an annual event into a continuous, real-time function. It creates a single source of truth, eliminating the confusion of scattered documents and inconsistent evidence.
Organizations that automate evidence collection and control mapping have reported reductions in audit preparation time by over 50%.
Gaining Real-Time Visibility and Control
Manual compliance data is often outdated as soon as it is recorded. Automation solves this by integrating with core systems to provide live data in dashboards that reflect the current security posture.
This continuous stream of information allows teams to identify compliance gaps or control failures as they occur and fix them before they escalate.
Key benefits include:
- Continuous Control Monitoring: The system tests controls 24/7 and sends alerts if a critical configuration changes or a policy is violated.
- Unified Control Mapping: A control can be defined once and mapped to multiple regulations (e.g., ISO 27001, SOC 2, GDPR). This "test once, comply many" approach reduces redundant work.
- Executive Dashboards: Leadership gets a clear, up-to-date view of organizational risk to support strategic decision-making.
A 2025 report indicated that 44% of organizations still rely on manual privacy assessments. However, adoption of RegTech automation is projected to reach 92% among EU financial firms by mid-2026. You can explore more of these findings in these data privacy and compliance statistics on partisia.com.
Answering Your Top Data Security Compliance Questions
This section addresses common questions about data security compliance.
We’re Just Starting Out. Which Compliance Framework Is Best?
For organizations building a compliance program from scratch, the NIST Cybersecurity Framework (CSF) is a recommended starting point. It is a flexible, risk-based guide that can be adapted to any business size or industry.
If formal, globally recognized certification is a goal, particularly for dealing with international partners, ISO 27001 is the standard. It is more prescriptive and guides the implementation of a certified Information Security Management System (ISMS).
How Do I Justify The Compliance Budget To The Board?
Frame the compliance budget discussion around risk reduction and business enablement, not just cost. Present a business case that quantifies the risks of non-compliance and connects the compliance program to strategic goals.
- It builds trust. Being a trusted custodian of customer data is a competitive differentiator.
- It unlocks new markets. A strong compliance posture is necessary for operating in regions with strict data protection laws.
- It accelerates sales. Enterprise customers often require proof of security, and a robust program can remove this barrier and shorten sales cycles.
According to a report from a European data protection authority, regulators issued $2.3 billion in GDPR fines in 2025, a 38% increase from the previous year. Between January 2024 and January 2025, 132,000 personal data breach notifications were filed, an average of 363 per day. These figures highlight the rising cost of inaction. You can find more details in these data privacy compliance trends on partisia.com.
What's The Single Biggest Mistake Companies Make With Compliance?
The most common mistake is treating compliance as a one-time project instead of an ongoing program. Regulations, cyber threats, and business processes are constantly changing. A "set it and forget it" approach leads to non-compliance and increased vulnerability.
Effective organizations integrate compliance into their culture. They achieve this through continuous monitoring, ongoing training, and automation that keeps them ahead of new requirements.
This approach transforms compliance from a reactive scramble into a sustainable business advantage.
Turn your data into a competitive advantage with enterprise-grade AI solutions from DSG.AI. Our integrated Responsible AI & GRC suite helps you meet governance standards and emerging regulations, ensuring your AI initiatives are both effective and compliant. Learn more about our production-ready AI projects.