Written by:
Editorial Team
Editorial Team
Third Party Risk Management (TPRM) is the process for identifying, analyzing, and controlling risks from working with external vendors and partners. It is a business strategy to ensure the companies you rely on do not create operational or security failures for your organization.
Understanding Third Party Risk Management
Imagine your business is a general contractor building a skyscraper. You hire specialist subcontractors for electrical, plumbing, and structural engineering. While they are the experts in their fields, your company is ultimately responsible for the safety and integrity of the entire building. If one subcontractor fails to meet standards, the entire project could be at risk.

This is how TPRM functions. In today's business environment, a security gap in one of your software vendors can become your organization's data breach. The security and operational stability of your organization are limited by the weakest link in your supply chain.
The Scope of Third Party Risk
TPRM is a broad discipline that extends beyond cybersecurity. It is a continuous cycle of evaluation that begins before a contract is signed and continues until the business relationship ends. A key part of this process involves What is vendor due diligence.
An effective TPRM program accounts for potential issues that could affect operations, finances, and public image.
A TPRM program provides organizations with a clear understanding of the third parties they use, how they use them, and the safeguards those partners have in place. It helps manage vendor relationships as strategic assets rather than potential liabilities.
To understand this better, we will examine the main categories of risk that a TPRM program must address. These are the core areas where a third party can introduce risk to your business.
The Core Domains of Third Party Risk
A TPRM framework is built around managing several distinct types of risk. The table below outlines these key areas.
| Risk Domain | Description | Example (Synthetic) |
|---|---|---|
| Cybersecurity | The risk of a data breach, malware infection, or system compromise originating from a third party. | A cloud provider with a misconfigured server exposes your customer data. |
| Operational | The risk that a third party’s failure to deliver a product or service will disrupt your business operations. | Your primary logistics partner experiences a system outage, halting your product shipments. |
| Compliance | The risk that a third party's actions will cause your organization to violate laws or regulations. | A marketing partner fails to comply with GDPR, resulting in fines for your company. |
| Financial | The risk that a third party’s financial instability could impact your business continuity or revenue. | A critical component supplier declares bankruptcy, forcing you to halt production. |
| Reputational | The risk that a third party's unethical behavior or negative publicity will damage your brand’s reputation. | A supplier is exposed for poor labor practices, leading to negative press for your brand. |
These domains show that TPRM is a business-wide function that protects the entire organization.
Your Attack Surface Is Larger Than You Think
Your company’s security perimeter is not limited to your physical or cloud environments. Each time you add a new SaaS vendor, integrate a partner’s API, or hire a marketing agency that handles customer data, your attack surface grows.
This network of partners, suppliers, and vendors is your digital supply chain. Each third party is a potential entry point into your organization. A single weak link can undermine a significant security investment. The consequences can include operational disruptions, regulatory fines, and damage to your brand's reputation.
The New Frontier of Risk: AI Supply Chains
The adoption of AI has added a new dimension to this problem. An AI supply chain includes the company that developed the algorithm, the firm that provides the training data, the platform that hosts the model, and the tools used for performance monitoring. This creates new vulnerabilities.
Consider these potential issues:
- Data Poisoning: A data supplier could intentionally or unintentionally provide corrupted information to your model. This could lead to inaccurate financial forecasts or biased automated hiring tools.
- Model Theft: Proprietary AI models are a competitive advantage. If a vendor with access to your models is breached, your intellectual property could be exposed, allowing a competitor to replicate your work.
- Evasion Attacks: Attackers can find vulnerabilities in a third-party AI component, feeding it inputs that trick your model. For example, a fraud detection system could be fooled, or a security filter could allow malicious content to pass.
These are business risks that auditors and regulators are beginning to investigate.
Quantifying the Third-Party Threat
Attackers often target suppliers as an indirect way to access your organization. When one of your vendors is breached, your data may be the target.
Third-party breaches are a significant source of security incidents across major industries. A single compromised vendor can serve as a gateway for attackers to access dozens or even hundreds of their clients, making the supply chain an efficient target.
Data shows this is a widespread issue. According to a 2024 report from SecurityScorecard and the Cyentia Institute, over half of all breaches in retail and hospitality (52.4%) now originate from a third party. The figures are similar in other sectors, with energy and utilities at 46.7% and tech and telecoms at 47.3%.
These statistics show that managing third-party risk is a core component of a security strategy. You can learn more about these supply chain breach statistics in the full report.
A Practical Look at the TPRM Lifecycle
Third-Party Risk Management is a continuous cycle, not a one-time task. Treating it as a simple background check at the start of a relationship is a common mistake. A mature TPRM program manages each vendor partnership through distinct stages to keep your organization safe.
This lifecycle ensures you identify risks before signing a contract, manage them throughout the partnership, and resolve all pending issues when the relationship ends. Each stage builds on the last, creating a layered defense against external threats.
With every new vendor, cloud service, or supply chain partner, your security perimeter expands, creating new potential entry points for attackers.
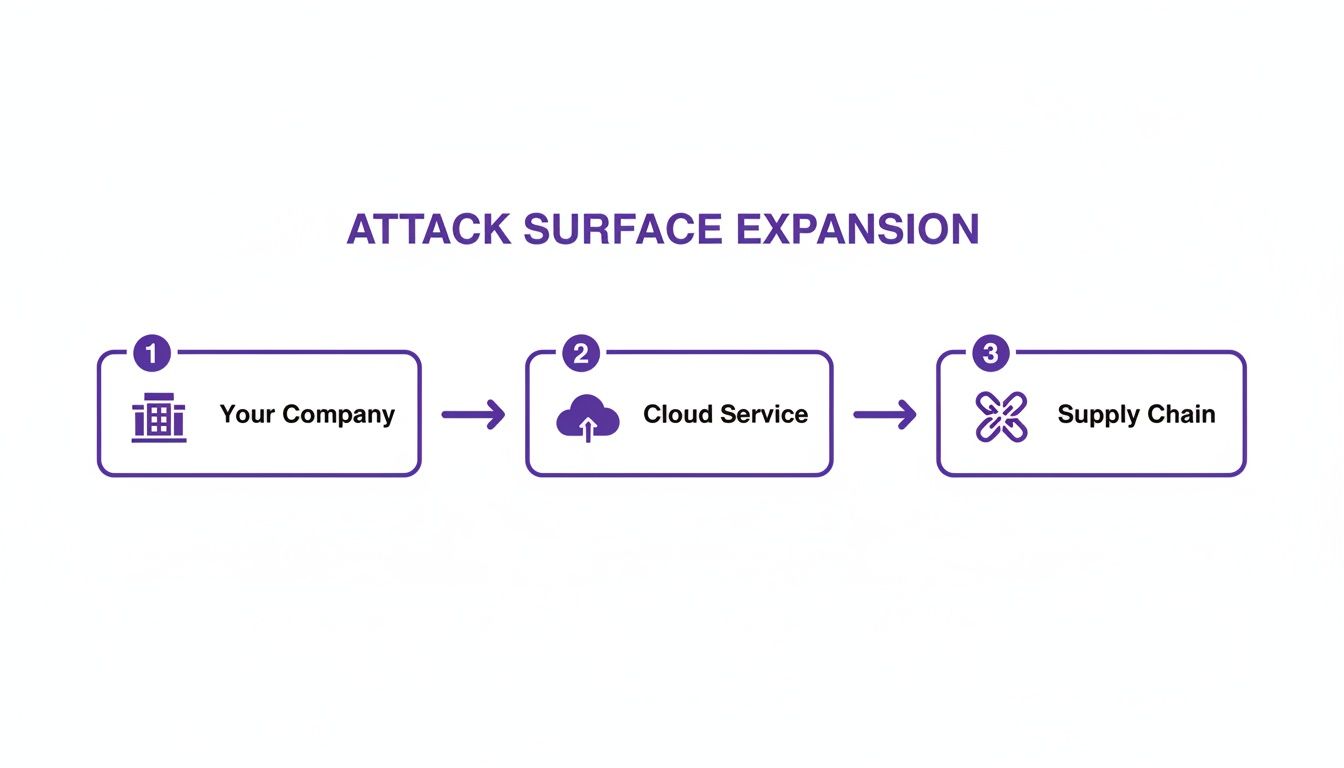
A structured, lifecycle approach provides the visibility and control needed to manage this growing attack surface.
Stage 1: Identification and Onboarding
This stage begins when someone in your organization identifies a need for a new vendor. It involves creating a central inventory and making a business case for the new partnership.
Key activities include logging the potential vendor, identifying the internal business owner, and defining the scope of work. This is your first line of defense, where you determine the vendor's criticality and what data they will access.
Stage 2: Due Diligence and Assessment
Once a vendor is identified as a potential fit, the investigation begins. This involves vetting their security, financial, and operational health before they access your systems or data. It validates their security claims.
This phase typically includes these steps:
- Sending Security Questionnaires: Using standard frameworks like NIST or SIG Lite to get structured answers about their controls.
- Reviewing Certifications: Asking for proof of compliance with standards such as ISO 27001 or SOC 2.
- Analyzing Financial Stability: You need to know if the vendor is financially sound. Their failure could create significant operational problems for you.
For complex AI systems, the vetting process is more specialized. It is important to assessAI vendors for unique risks to ensure their models and data handling practices meet your governance standards.
The purpose of due diligence is to uncover risks before they become your problem. It shifts the vendor relationship from one based on trust to one built on evidence.
Stage 3: Contracting and Remediation
After the assessment, you will likely find gaps between your security requirements and the vendor's current posture. This stage is about closing those gaps, using the contract as an enforcement tool.
For instance, if an assessment finds that a vendor is not using multi-factor authentication on a critical system, you can require them to fix it before signing the contract. Alternatively, you can add a clause to the agreement that obligates them to remediate the issue within a specific timeframe, such as 90 days. This makes security a contractual requirement.
Stage 4: Continuous Monitoring
A vendor’s security posture can change quickly. An effective TPRM program uses continuous monitoring instead of annual check-ins. This means you actively watch for any changes that could indicate a problem.
This is often done with automated tools that scan for new vulnerabilities, monitor for negative press, or track security ratings. If a high-risk vendor has a critical port exposed or is named in a data breach, you will be notified in near real-time, not at the next annual review.
Stage 5: Offboarding
When a contract ends, the relationship must be terminated securely. Offboarding involves revoking all access credentials, ensuring your sensitive data has been returned or destroyed, and confirming that all contractual obligations are met.
A proper offboarding process prevents "ghost access," where a former vendor’s login credentials remain active on your network. These accounts represent an unnecessary risk. This final stage provides a clean, documented end to the partnership.
Moving Beyond Spreadsheets and Annual Reviews
Relying on static spreadsheets and annual vendor reviews is a common failure point in modern risk management. These methods create a false sense of security in an environment where a vendor’s risk profile can change rapidly.
An annual questionnaire is a snapshot in time. A vendor might pass an assessment in January but become the source of a breach in July. A reactive approach means you often learn about a critical risk after the damage has occurred, putting your team in a constant state of response.
Shifting to a Dynamic Defense
To manage third-party risk effectively, you must move beyond a static mindset. A good starting point is to base your program on a framework like the NIST Cybersecurity Framework (CSF) or ISO 27001. These provide a structured language for assessing and discussing risk.
A modern program uses these frameworks as a foundation for continuous validation. This involves using technology to get a near real-time view of your vendors' environments.
This is becoming a necessity as regulatory focus increases. A 2024 Ncontracts survey found that nearly 50% of financial institutions experienced a vendor-related cyber event in the previous year. As a result, two-thirds of them report increased pressure to improve their TPRM programs. You can discover in the full TPRM survey findings, these incidents are leading to larger budgets and program expansions.
The Power of Continuous Monitoring
The core of a modern TPRM strategy is continuous monitoring. This uses automated tools to keep a constant pulse on the risk levels across your vendor ecosystem, transforming risk management from a periodic audit into an ongoing, automated process.
This includes:
- Security Ratings Services: These platforms continuously scan your vendors' external-facing systems, flagging issues like open ports, malware infections, and insecure configurations. They provide an objective, data-driven view of their security health.
- Automated Evidence Collection: Modern platforms can connect to vendor systems to automatically verify controls, such as confirming that security patches are applied or new hires have completed security training. This type of TPRM orchestration reduces manual work and provides more reliable data.
- Threat Intelligence Feeds: These services alert you if a vendor appears in dark web discussions, is named in a new breach report, or is dealing with a public cyber incident. This external view helps you spot threats early.
Adopting a continuous monitoring model changes your security posture from reactive to proactive. You no longer wait for a vendor to report a problem. You have the data to see emerging risks and address them before they escalate.
How to Build a Scalable TPRM Program
Building a scalable TPRM program requires a blueprint that combines strong governance with the right technology. Without both, TPRM efforts can fail when managing hundreds or thousands of vendors.
The process begins with a solid foundation of governance. This means establishing clear rules, defining roles and responsibilities, and determining your organization's risk appetite—how much risk you are willing to accept from a partner.
This governance model must be integrated into your procurement process from the beginning. When a risk assessment becomes a required step before any contract is signed, you can prevent risky relationships before they start.
Establishing Strong Governance
To build a TPRM program that can scale, you need effective IT compliance and risk management strategies. This framework ensures consistency and accountability.
First, create a cross-functional TPRM committee with leaders from IT, security, legal, procurement, and key business units. This team will guide the program, approve risk tolerance levels, and make final decisions on high-risk vendor issues.
With this team in place, you can focus on three core governance activities:
- Defining Risk Tiers: Not all vendors carry the same level of risk. Segment them into tiers—such as Critical, High, Medium, and Low—based on their access to sensitive data and their importance to your operations. This allows you to focus your due diligence efforts where they are most needed.
- Standardizing Assessments: Create a standard set of security questionnaires and assessment procedures for each risk tier. A critical payment processor will require a higher level of scrutiny than the company that supplies your office coffee.
- Integrating with Procurement: Build checkpoints into the procurement workflow. For example, a rule that states, "No purchase order is issued for a high-risk vendor until the TPRM team has signed off," is a simple but effective control.
The Critical Role of Tooling and Automation
Governance defines the "what" and "why," but technology provides the "how," especially at scale. Manual processes cannot keep up with a modern vendor ecosystem. Modern GRC (Governance, Risk, and Compliance) platforms are essential.
These tools can transform TPRM from a manual task into an automated function. They provide a single source of truth for all vendor data, assessments, and communications. For more on this, you can read our guide on how to manage AI to meet governance standards. https://dsg.ai/manageai
Despite the growing adoption of TPRM programs, confidence remains low. A 2024 survey from the Ponemon Institute shows that only 34% of organizations are confident their programs can effectively manage third-party threats in real time. This is often due to manual approaches; only one in three companies continuously monitors all their third-party relationships for new risks.
Automation is the only viable path to achieving real-time risk visibility. It allows your team to shift its focus from administrative tasks to making strategic, data-driven decisions that protect the business.
Key features in modern TPRM platforms that enable scaling include:
- Automated Risk Scoring: These platforms can automatically calculate a vendor’s inherent risk score during onboarding. This places the vendor in the correct tier and initiates the appropriate assessment workflow without manual intervention.
- Centralized Dashboards: Stakeholders get a real-time, consolidated view of the risk posture across the entire vendor portfolio.
- Streamlined Workflows: Automation handles administrative tasks like sending assessment reminders and tracking remediation, ensuring nothing is missed.
This combination of clear governance and smart automation allows a TPRM program to grow with your business, demonstrate due diligence to regulators, and provide actionable insights to your board.
What to Do Next: Your TPRM Maturity Roadmap
Managing third-party risk is a core business function. In a world where your supply chain is both digital and physical, you need a modern, automated way to manage risk.
The transition from theory to practice does not have to happen all at once. A mature TPRM program is built incrementally, starting with the areas that pose the greatest threat.
A Foundational Action Plan
A manageable plan that shows results quickly can build momentum and gain leadership support. This practical approach can demonstrate the value of TPRM and justify further investment.
Here is a simple, three-step plan to get started:
-
Map and Rank Your Vendors: Create a complete inventory of every third party you work with. Then, rank them based on risk. A vendor that processes customer payments is in a different risk category than your office coffee supplier.
-
Run a Continuous Monitoring Pilot: Select a small group of your highest-risk, Tier 1 vendors. Start a continuous monitoring process for this group to get a live view of their security posture. This focused experiment can demonstrate the limitations of static, annual reviews.
-
Investigate Specialized TPRM Platforms: After proving the concept on a small scale, you will have the evidence needed to build a business case for a broader program. Explore dedicated TPRM platforms to see how you can automate assessments, streamline workflows, and get a clear view of your entire vendor ecosystem.
This phased approach turns TPRM from an abstract idea into a concrete, value-adding function. It focuses on addressing your biggest vulnerabilities first, then building a framework that can scale.
Following a structured process like this reduces immediate risk and builds the operational capacity for a resilient, enterprise-wide program. As regulations like the EU AI Act become more complex and supply chains expand, a scalable, automated system is essential.
Getting Your Questions Answered on TPRM
Even with a good understanding of the TPRM lifecycle, implementation often raises specific questions. Here are a few common ones.
What's the Real Difference Between TPRM and Vendor Risk Management?
These two terms are often used interchangeably, but there is an important difference.
Vendor Risk Management (VRM) focuses on the suppliers you purchase from—those with whom you have a procurement relationship. It is a critical component, but it does not cover the entire scope of third-party risk.
Third-Party Risk Management (TPRM) is a broader term that covers your entire ecosystem of external relationships. This includes not just vendors, but also strategic partners, contractors, affiliates, and the "fourth parties" that your vendors rely on. In short, VRM is a discipline that operates within a larger TPRM strategy.
With So Many Partners, How Do We Decide Who to Assess First?
Effective programs do not treat every partner the same. The key is risk tiering—a method for sorting your third parties based on their criticality to your business and the sensitivity of the data they handle. This ensures you focus your resources where they matter most.
A common tiering model is:
- Tier 1 (High-Risk): These are essential partners, such as the payment processor that handles all your customer transactions or the cloud provider that hosts your core applications. A failure here directly impacts your business, so they receive the highest level of scrutiny.
- Tier 2 (Medium-Risk): This tier includes partners who may access some sensitive data but are not essential for daily operations.
- Tier 3 (Low-Risk): Your office supply company or landscaping service likely falls into this category. These relationships require minimal oversight.
By tiering your third parties, you can allocate your resources more efficiently. It allows you to right-size your due diligence efforts, applying the most scrutiny to the relationships that pose the greatest potential threat.
We're on a Tight Budget. Can We Still Pull This Off?
Yes. You do not need a large, fully automated system from day one. Start with foundational steps that provide significant value without a large investment.
Begin by creating an inventory of all your partners; a detailed spreadsheet is a sufficient starting point. Then, develop a standard security questionnaire for new high-risk partners. At the same time, work with your legal team to add "right-to-audit" clauses to new contracts. These simple actions establish a baseline of control. The cost of a breach is almost always far greater than the cost of implementing a basic program.
At DSG.AI, we help enterprises build scalable, automated GRC and TPRM programs that address the complexities of modern digital supply chains, including emerging AI regulations. Learn how we can help you turn risk management into a strategic advantage by exploring our enterprise AI solutions.