Written by:
Editorial Team
DSG.AI
Operational risk is the potential for financial loss resulting from inadequate or failed internal processes, people, and systems or from external events. It is not the risk of a market downturn or a failed business strategy. It is the risk of failure from within your daily operations.
This guide defines operational risk, identifies its primary sources, and outlines a practical framework for managing it.
What Is Operational Risk

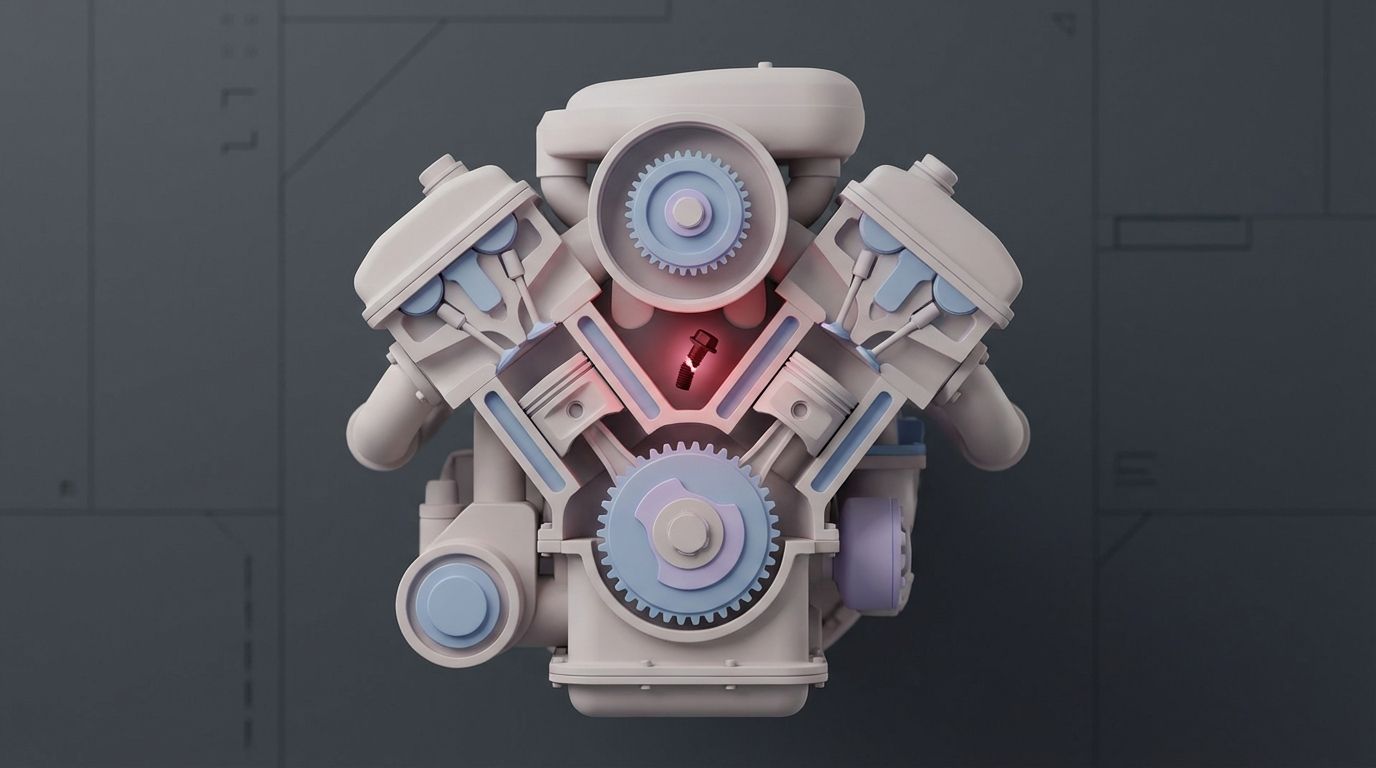
Consider your company as an engine. Market risk is like hitting an unexpected patch of ice on the road. Credit risk is the chance that a supplier fails to deliver a critical part.
Operational risk is the danger of a bolt shearing off inside the engine. It could be a faulty part (a broken process), an oversight by a technician (human error), or a software glitch in the diagnostic system (a system failure). These are failures of execution, not strategy.
The Formal Definition and Why It Matters
The concept was formalized by the Basel Committee on Banking Supervision to create a standard framework. Their definition is "the risk of loss resulting from inadequate or failed internal processes, people and systems or from external events."
This definition originated in banking but now applies to every industry. It acknowledges that internal failures—from employee mistakes and internal fraud to cyberattacks—can cause significant financial and reputational damage. For many banks, operational risk is the second largest risk category after credit risk. You can learn more about why this risk matters for financial institutions.
In short, if you do not manage operational risk, you leave your company's core functions exposed to preventable failures. Effective management ensures the engine runs reliably and without unexpected breakdowns.
Breaking Down the Core Sources
To manage operational risk, you must understand its sources. Every potential failure can be traced to one of four areas.
The table below outlines these four pillars with a definition and a synthetic example for each.
The Four Core Pillars of Operational Risk
| Pillar | Definition | Synthetic Example |
|---|---|---|
| People | Risks from human actions, including accidental errors, intentional misconduct, or skill deficiencies. | An employee clicks on a phishing email, which gives an attacker access to company data. |
| Processes | Flaws or gaps in internal procedures, workflows, and controls that create vulnerabilities. | A company lacks a formal process for approving large payments, leading to an unauthorized transfer. |
| Systems | Failures related to technology, including software bugs, hardware malfunctions, or security vulnerabilities. | A critical server fails during peak business hours due to improper maintenance, causing a company-wide outage. |
| External Events | Incidents outside of your direct control that disrupt operations. | A major storm floods a data center, knocking out a company's primary website and services. |
By categorizing operational risk into these four areas, you can move from a general concern to a structured approach for identifying and addressing specific threats. This foundation is the first step toward building a more resilient organization.
The Four Primary Categories of Operational Risk

To manage operational risk, you must know where it originates. Every internal failure, from a data entry typo to a system shutdown, can be traced to one of four categories. Analyzing risk this way transforms it from a vague threat into a specific, actionable problem.
Use these categories—People, Processes, Systems, and External Events—as a framework for identifying weak points in your daily operations. Each represents a unique area where failures can occur and often trigger cascading effects across the organization.
People Risk
The human element is often the most unpredictable variable. This category covers failures stemming from human action, inaction, or error. It ranges from an unintentional mistake to a malicious act.
People risk also includes talent and knowledge gaps. For example, if a senior engineer with 15 years of institutional knowledge leaves without documenting the critical systems they built, that creates a significant risk. The remaining team must maintain or fix that software without complete information, which can lead to extended downtime.
Here are three examples of people risk:
- Insufficient Training: An employee mishandles sensitive customer data due to inadequate training on privacy regulations, leading to a compliance violation.
- Human Error: A finance clerk accidentally wires $1,000,000 instead of $10,000. The financial loss is immediate, and recovery can take days.
- Internal Fraud: A manager with excessive system permissions approves fake invoices for a shell company they control.
Process Risk
This category involves failures in the design or execution of internal workflows and procedures. A flawed process creates an environment where errors are more likely to occur. These risks are embedded in the way your business operates.
Consider a manufacturing line with a weak quality control process. One failed checkpoint could allow thousands of defective products to pass, leading to a product recall and brand damage. The failure was not one person's fault; it was a systemic breakdown in the approved workflow.
A well-designed process acts as a guardrail, guiding employees toward the correct outcome and making it difficult to commit critical errors. When these guardrails are missing or broken, operational risk increases.
Systems Risk
Systems risk covers any failure related to your technology, including hardware, software, networks, and data security. In a modern business, a single system failure can halt all operations.
Imagine an e-commerce site whose servers crash on Black Friday. The direct revenue loss is calculable, but the damage also includes customer frustration and long-term brand erosion. Such failures often result from deferred maintenance, unpatched security vulnerabilities, or inadequate capacity planning.
External Events and Third-Party Risk
Some of the most disruptive operational risks originate outside your company. These are events you cannot control but must prepare for, such as natural disasters, political instability, or sudden regulatory changes. A significant component of this is third-party risk.
A new tariff on a key component can disrupt your entire supply chain, stopping production and delaying customer orders. Similarly, if your primary cloud provider experiences a major outage, it can take your core services offline, even if your internal systems are functioning correctly. Managing these interconnected threats is a specific discipline. To learn more, read our detailed guide on Third-Party Risk Management.
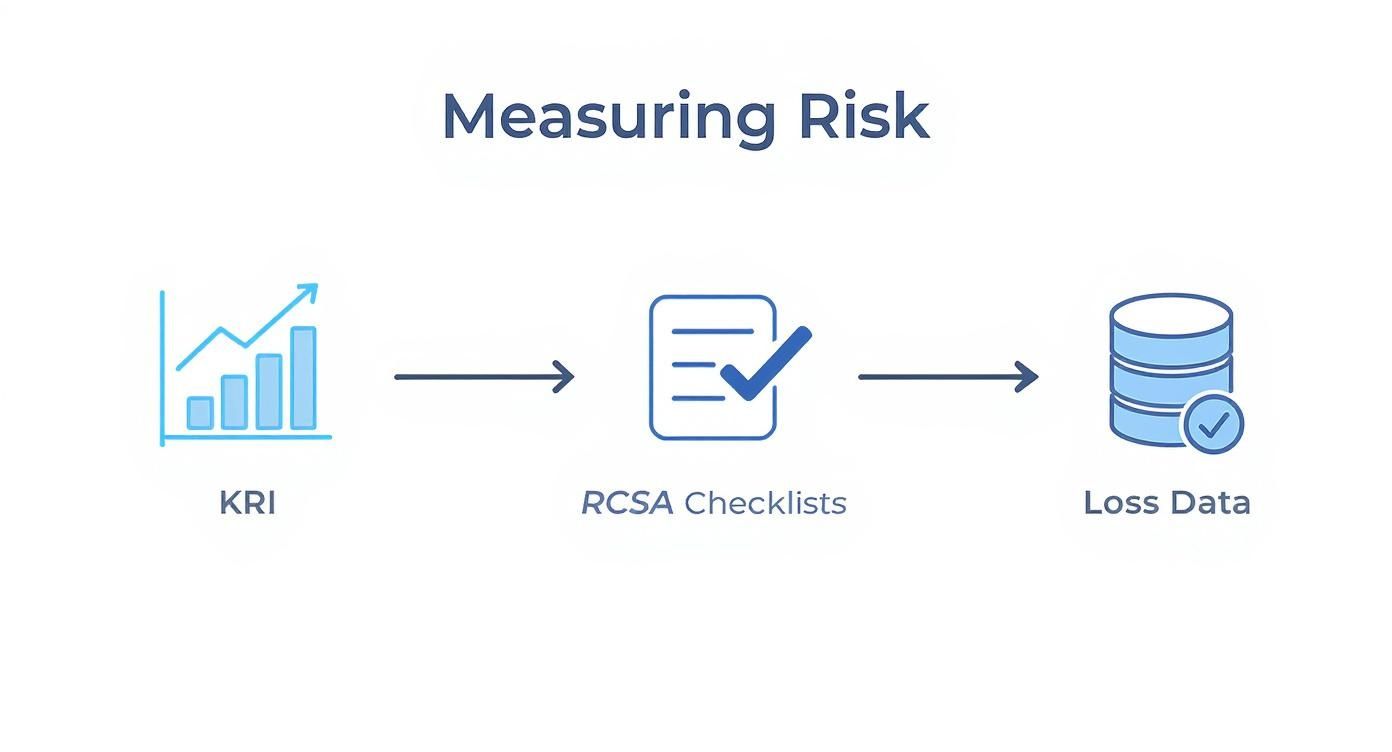
How to Measure Operational Risk
Operational risk can seem like an abstract threat that is difficult to quantify. However, you cannot manage what you do not measure. Resilient organizations use specific tools to translate this risk into concrete data, which supports better decision-making.
This is not about waiting for something to break. It is about building an early warning system. By monitoring the right signals, teams can identify problems before they escalate into operational failures.
Using Key Risk Indicators as Early Warnings
Key Risk Indicators (KRIs) are specific, measurable metrics designed to provide an early warning that risk is increasing in a particular area. When a KRI crosses a predefined threshold, it triggers an investigation before a significant incident occurs.
Effective KRIs are directly tied to business objectives and provide actionable information. Here are three synthetic examples:
- Employee Turnover Rate: A sudden increase in turnover in a critical department can signal people-related risks like knowledge loss or low morale. You might set a baseline at a 4% quarterly turnover rate, with an alert triggered if it reaches 7%.
- Unplanned System Downtime: Tracking the number of minutes or hours a key application is offline can reveal underlying system issues. A steady increase in downtime is a common sign of aging infrastructure or unstable software.
- Number of Open IT Security Patches: This KRI is a direct measure of your vulnerability to cyberattacks. As the backlog of overdue patches grows, so does your systems risk.
Capturing Insights with Assessments and Loss Data
In addition to monitoring metrics, two other practices are essential for a complete view of operational risk.
The first is the Risk and Control Self-Assessment (RCSA). This is a structured process where business units identify and evaluate the operational risks in their daily work. It is an effective method for tapping into the knowledge of front-line employees, who often uncover vulnerabilities that a central risk team might miss.
The second is Loss Data Collection. This involves systematically recording every operational loss event, regardless of its size. Tracking a series of minor data entry errors in one department could indicate a flawed process or a training gap. Over time, this historical data helps predict future vulnerabilities and justifies investments in improved controls.
Collecting reliable data presents challenges. Not all losses are reported publicly, which can bias external databases. This often leads to an overrepresentation of large, infrequent losses while smaller, more frequent events are missed. Building an accurate risk model requires careful data analysis, as detailed in this paper on analyzing operational risk loss data.
By combining KRIs, RCSAs, and loss data, you create a multi-dimensional view of your operational risk landscape. This approach transforms risk management from an intuitive exercise into a strategic discipline, providing leaders with the hard data needed to conduct a proper internal control audit and allocate resources effectively.
Building Your Operational Risk Management Framework
You cannot manage operational risk with reactive, one-off fixes after an incident. Effective operational risk management is a systematic, continuous discipline built on a solid framework.
This foundation is often called an Enterprise Risk Management (ERM) framework. It is a blueprint that transforms risk management from a collection of disconnected tasks into a cohesive function that supports business goals.
The adoption of formal ERM is a proven strategy. A 2021 study by the Association for Financial Professionals (AFP) found that 76% of organizations had a formal or in-process ERM program. Organizations with mature ERM programs report benefits such as a 15% reduction in compliance costs and a 10% increase in profitability, according to a 2019 report by COSO. A structured approach delivers measurable results.
The Core Risk Management Cycle
A strong framework is not a checklist you complete once. It is a continuous cycle with four key stages. This loop shifts an organization from a reactive mode—constantly addressing crises—to a proactive posture where threats are neutralized before they cause damage.
Here is how the cycle works:
-
Identify: The first step is to find and document potential failures. This involves process mapping, conducting brainstorming sessions with front-line employees, and analyzing past incidents to uncover hidden weaknesses.
-
Assess: Once a risk is identified, you must determine its significance. This involves analyzing its potential impact and likelihood of occurrence. The goal is to prioritize risks to focus resources where they are most needed.
-
Mitigate: This is the action stage. Based on a prioritized list of risks, you develop strategies to either reduce the likelihood of a risk occurring or lessen its impact. Mitigation can include implementing new security controls, automating a manual process, or creating a disaster recovery plan.
-
Monitor: Business conditions and risks change. The final stage is continuous oversight. You need to track known risks, verify that your controls are effective, and scan for new threats. Many organizations are implementing continuous monitoring to get ahead of issues. Integrated platforms like assureIQ can automate GRC monitoring, providing a real-time view of your entire risk posture.
This workflow shows how measurement activities—such as tracking KRIs, conducting control assessments, and analyzing loss data—are integrated into the assessment and monitoring phases.
By bringing these elements together, a good framework provides a complete, data-driven view of your organization's risk landscape. Risk management becomes a strategic advantage instead of a cost center.
Learning from Real-World Operational Failures
Case studies of major corporate failures provide powerful lessons in operational risk. By analyzing these events, we can see how a seemingly minor internal issue can escalate into a catastrophe.
Moving from abstract concepts to concrete examples makes operational risk easier to understand. Each case study reveals that the categories of People, Processes, Systems, and External Events are often interconnected.
A Data Breach from People and System Failures (Synthetic Example)
Consider a data breach caused by a combination of System and People risk. It began with a phishing email sent to an employee—a common human vulnerability. The employee had not received security awareness training recently and clicked a malicious link.
This single human error allowed attackers to exploit an unpatched vulnerability on a web application server, a clear System failure. The company's patch management process was inconsistent, leaving a known security hole exposed for months. The result: the personal information of over 100 million customers was stolen, leading to regulatory fines exceeding $150 million and significant, long-lasting brand damage. This synthetic example shows how a simple human mistake combined with a weak system control can lead to a devastating outcome.
Supply Chain Collapse Due to External Events (Synthetic Example)
Another example comes from an automotive manufacturer whose production lines halted. The immediate cause was an External Event: a fire at the factory of a single, specialized microchip supplier.
The fire was not the true operational failure. The breakdown was the company's own flawed sourcing process. By single-sourcing a critical component with no backup plan, they created a single point of failure in their supply chain.
This lack of supplier diversity, a significant Process risk, caused assembly lines for their most profitable vehicles to stop for nearly two quarters. The financial impact was substantial, with revenue losses estimated in the billions. By failing to manage its third-party concentration risk, the company turned its supplier's crisis into its own operational catastrophe.
Internal Fraud Enabled by Process Breakdowns (Synthetic Example)
Finally, consider a common scenario of internal fraud—a combination of People and Process risk. A manager in a company's procurement department observed that invoices under $10,000 did not require secondary approval. This process gap was an opportunity for fraud.
The manager created a shell company and began submitting fake invoices, each just under the review threshold. Over 18 months, they diverted nearly $750,000 before an unrelated audit discovered the scheme. The failure was twofold: an individual with malicious intent and a poorly designed approval process lacking basic controls. The direct financial loss was significant, but the damage to internal trust and the cost of redesigning the procurement system were even greater.
Each of these synthetic stories illustrates that operational risk is a tangible result of failures in daily business operations.
Your Action Plan for Mitigating Operational Risk
Understanding the theory of operational risk is the first step. The next is to defend your organization through concrete action. A smart starting point is often understanding how to reduce operational costs, as financial waste and operational vulnerabilities are frequently linked.
This five-step plan is designed for CIOs, CTOs, and risk leaders who need to build operational resilience. These are immediate next steps to build momentum and foster a culture that takes operational risk seriously.
A Practical Checklist for Leaders
Focus on high-impact activities you can start now. For each item, I will explain its importance and provide a clear first step.
-
Establish Clear Risk Ownership
- Why it matters: Accountability is essential in risk management. If a risk has no owner, no one is responsible for managing it. Assigning a specific leader to each major operational risk, such as cybersecurity or system uptime, ensures accountability and drives action.
- Your first step: Meet with your leadership team to identify your top five operational risks and assign a specific owner for each. Document these assignments in a risk register.
-
Conduct a Risk Identification Workshop
- Why it matters: You cannot manage risks you have not identified. The most effective way to map your organization's vulnerabilities is to involve front-line managers and process owners. They have direct knowledge of the gaps, workarounds, and inefficiencies that can signal larger problems.
- Your first step: Schedule a 90-minute workshop with key leaders from IT, Operations, and Finance. The purpose is to brainstorm potential failures in their respective domains and discuss the business impact of each.
-
Develop Three Initial Key Risk Indicators (KRIs)
- Why it matters: KRIs are an early-warning system for operational failures. Tracking the right metrics provides objective data on rising risk levels before an incident occurs, shifting your team from reactive to proactive.
- Your first step: Start with three straightforward KRIs. Good examples include 'unplanned system downtime,' 'number of help desk tickets for access issues,' or 'percentage of overdue security patches.'
A 'no-blame' culture is essential. When people feel safe reporting near-misses and small errors without fear of punishment, leaders gain an unfiltered view of process weaknesses before they become crises.
-
Promote a 'No-Blame' Reporting Culture
- Why it matters: Fear inhibits transparency. When employees are afraid to admit mistakes, you lose valuable opportunities to learn and improve. A culture that encourages open reporting of issues creates a continuous stream of intelligence on process breakdowns.
- Your first step: In your next company-wide meeting, publicly recognize an employee who identified and reported a potential issue. Thank them for their vigilance and for helping the company improve. Make it clear this is the desired behavior.
-
Automate One Key Manual Control
- Why it matters: Repetitive manual tasks are prone to human error. Automating a single critical control—such as user access reviews or data validation—can reduce errors by over 90% based on common industry observations. It also frees up employees for more strategic work.
- Your first step: Identify a single, high-volume, rules-based manual task that is known for errors. Make it a priority project to automate that process within the next quarter.
Wrapping Up: Your Operational Risk Questions Answered
As you formalize your approach to operational risk, several common questions often arise. Here are straightforward answers.
Operational Risk vs. Strategic Risk: What’s the Real Difference?
The distinction is important. Operational risk is about execution—the potential for failures in day-to-day activities, such as flawed processes, human error, or system outages.
Strategic risk is about the danger of choosing the wrong business plan.
Here is a simple analogy: as the captain of a ship, an operational risk is the engine failing mid-voyage. A strategic risk is setting your course for the wrong continent. One is a failure in doing things right; the other is a failure in doing the right things.
How Can a Small Business Tackle Operational Risk Without a Big Budget?
You do not need a large GRC department to manage operational risk. For smaller businesses, focus on fundamentals and smart habits.
Start by mapping your most critical processes. Document who does what and where handoffs occur. Then, introduce simple controls, like the "four-eyes principle" for payments—one person prepares it, and a second person approves it. Regular cybersecurity awareness training is another low-cost, high-impact action. The focus should be on building a risk-aware culture rather than buying expensive software.
Is Compliance Risk Just Another Name for Operational Risk?
No, but they are closely related. Compliance risk is a subset of operational risk. Compliance risk is the threat of legal penalties, fines, or reputational damage from failing to follow laws, regulations, or internal policies.
Why do those compliance failures happen? Almost always, the root cause is a breakdown in internal processes, inadequate employee training, or a system that cannot enforce the rules. These are all sources of operational risk.
DSG.AI helps enterprises build robust, AI-driven risk management frameworks. Our GRC automation and custom AI solutions provide the visibility and control needed to turn risk management into a competitive advantage. Discover our enterprise-grade AI projects at https://www.dsg.ai/projects.