Written by:
Editorial Team
DSG.AI
The global average cost of a data breach is $4.44 million, according to IBM's 2023 report. For a business leader, this number represents a direct threat to profitability and shareholder value. The total financial impact is a complex mix of direct expenses, regulatory penalties, and long-term business damage that can persist for years.
Understanding this financial reality is the first step in justifying security investment before an incident occurs, not just after.
The most recent data shows a 9% decrease from a record high of $4.88 million to $4.44 million. This is largely because companies are improving their ability to detect and contain threats faster. However, the financial risk remains significant.
A Closer Look at the Core Numbers
Even with quicker response times, the average cost for each compromised record is approximately $160.
Certain industries are impacted more severely. Healthcare, for example, continues to have the highest average breach cost at $10.93 million. This highlights how factors like regulatory compliance and data sensitivity can multiply the final cost.
The total cost of a data breach is not a single event. It is a cascade of expenses that unfolds over months, and sometimes years, impacting everything from the operational budget to brand reputation and customer trust.
This summary provides a high-level view of the key financial metrics.
Summary of Average Data Breach Costs
This table breaks down the typical financial impact from a data breach, based on 2023 global averages from IBM.
| Metric | Average Cost | Key Driver |
|---|---|---|
| Total Breach Cost | $4.44 million | Overall financial impact on the organization. |
| Cost Per Record | $160 | The value assigned to each lost or stolen record. |
| Healthcare Breach | $10.93 million | Industry-specific costs driven by compliance & data sensitivity. |
These numbers show that inadequate security is a guaranteed future expense. The components that make up these totals can be grouped into four key areas. Breaking down the costs this way clarifies the multi-million-dollar figure and shows where proactive security measures can deliver the greatest financial savings.
The Anatomy of a Data Breach Bill: Where Does the Money Go?
The cost of a multi-million dollar data breach is not a single invoice. It is a series of expenses that accumulate across different stages of the crisis. It is less like a one-time fine and more like a financial storm with a long, damaging tail.
Breaking down where the money is spent is the first step to understanding how much proactive security measures can save the business.
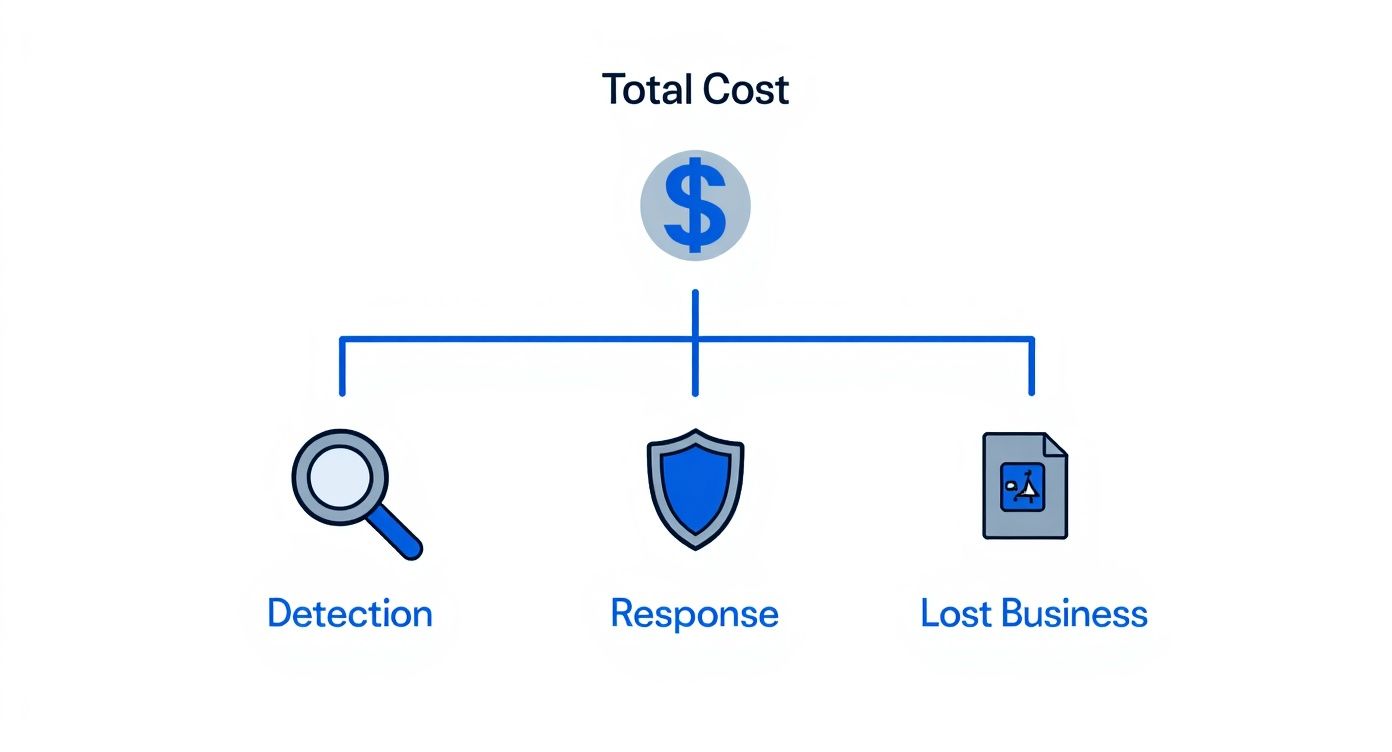
As the diagram shows, the immediate cleanup is just the beginning. The largest financial impact often comes from lost business—the slow, lingering damage that can cripple a company long after the breach is contained.
Detection and Escalation: The First 48 Hours
The moment a breach is suspected, the clock starts ticking, and so does the meter. This first phase is a race to answer critical questions: Are we breached? How did they get in? What did they take? The costs here are immediate and they accumulate quickly.
This initial scramble involves:
- Digital Forensics: Third-party experts may be required to analyze logs, reverse-engineer malware, and trace the attackers' movements. These specialists can charge tens of thousands of dollars per day.
- Internal Overtime: Your own IT and security teams will be working around the clock. Those overtime hours are a direct, tangible cost.
- Assessment Services: Often, another firm is needed to assess the full scope of the damage and identify the compliance failures that led to the attack.
The financial bleed starts long before the public is aware of the incident. In fact, a significant portion of all breach-related costs are incurred within the first year. Organizations with a security skills shortage can expect those costs to be higher, a stark reminder of the value of having the right expertise. You can get more insights on how talent impacts breach costs from the experts at Spacelift.io.
Notification and Response: The Cleanup Crew
Once a breach is confirmed, a new set of expenses begins. This phase is about communicating with regulators, customers, and the public while managing the immediate chaos. Mishandling this stage can lead to large fines and destroy customer trust.
Thinking of notification as just sending an email is a common mistake. It is a complex process with legal requirements, tight deadlines, and stakeholder management that can go wrong in multiple ways.
Expenses in this stage accumulate quickly:
- Specialized Legal Counsel: You will need lawyers who specialize in data privacy laws to navigate the complex web of state, federal, and international regulations.
- Regulatory Filings: Preparing and submitting the required notifications to bodies like the SEC, FTC, or GDPR authorities is a resource-intensive process.
- Crisis Communications: A PR firm specializing in crisis management is often essential to control the narrative and protect your brand from permanent damage.
- Victim Support: The direct costs of providing credit monitoring, identity theft protection, and call center support for every affected individual can be substantial.
The Heavy Toll of Lost Business: The Long Tail
The fourth and final cost center is often the most devastating: lost business. This is the long-term financial fallout that can affect a company for years. It is the most difficult cost to quantify, but it is almost always the largest portion of the total expense.
This slow drain on the bottom line comes from several key areas:
- Customer Churn: Trust is fragile. Once it is broken, customers may leave for competitors and may not return.
- Reputation Damage: Negative press makes it more difficult to win new business. Your brand becomes associated with risk.
- Business Interruption: While your teams are managing the crisis, normal operations are disrupted. Every hour of downtime is an hour of lost revenue.
- Increased Insurance Premiums: After filing a claim for a breach, your cybersecurity insurance provider will likely raise your rates significantly, if they agree to renew your policy at all.
Consider the case of Equifax. Beyond the $1.38 billion in fines and settlements from its 2017 breach, the company also saw its financial rating downgraded by Moody's. This is a clear example of how the consequences of a breach can impact a company’s financial health for years.
How Location and Industry Drive Breach Costs
The global average cost of a data breach is a useful starting point, but it does not provide the full picture. The location of your business and your industry can significantly change the financial outcome of a security incident. These are powerful cost multipliers that can double or even triple the final bill.
Think of it like a storm. A hurricane hitting a sparsely populated coastline will cause damage. The same storm hitting a dense, major city creates a catastrophe. A data breach in a less-regulated industry might be a manageable problem, while the same breach in a highly regulated sector like U.S. healthcare is a financial disaster.
To understand your risk, you must look past global averages and consider the specific pressures of your geography and industry.
The Geographical Cost Divide
Different countries approach data privacy with varying levels of regulatory enforcement. This creates a large gap in the cost of a data breach depending on where you operate. The United States has consistently been the most expensive place in the world to experience a data breach.
The average cost of a data breach in the U.S. recently reached $9.48 million in IBM's 2023 report. This is the highest of any region and is largely driven by state-level privacy laws and a mature, expensive market for incident response services. The cost per compromised record in the U.S. is also the highest at $264, underscoring the intense regulatory pressure. You can dig deeper into these regional cost differences in this TotalAssure.com analysis.
What is behind these large geographical differences?
- Regulatory Frameworks: Europe's GDPR can impose fines based on a percentage of a company's global revenue. The U.S. has a complex patchwork of federal and state laws, like California's CCPA/CPRA, each with its own notification rules and penalties.
- Litigation Culture: The probability of facing a class-action lawsuit after a breach is far higher in some countries, which can add millions in legal fees and potential settlements.
- Market Maturity: In regions with well-established cybersecurity and legal industries, the top-tier forensic investigators, lawyers, and crisis communication firms simply cost more.
Why Your Industry Is a Major Cost Factor
Just as location shapes the cost, your industry dictates the value and sensitivity of the data you hold—which directly impacts the financial fallout from a breach. If you are in a highly regulated industry, you face a double challenge: the data you protect is a prime target for attackers, and the penalties for failing to protect it are more severe.
A patient's electronic health record is not the same as a retail customer's shipping address. The intrinsic value of the data, combined with strict compliance mandates, creates a perfect storm for higher breach costs.
For over a decade, healthcare has remained the most expensive industry for a data breach, with costs that are significantly higher than other sectors. The financial services and pharmaceutical industries are also among the most affected.
The table below provides a snapshot of how these costs can vary, offering a clearer view of the financial risk depending on your location and industry.
Data Breach Costs by Region and Industry
| Region / Industry | Average Breach Cost | Key Cost Driver |
|---|---|---|
| Healthcare | Over $10 million | HIPAA compliance fines and highly sensitive patient data |
| Financial Services | Over $6 million | Heavy regulatory penalties and the critical loss of customer trust |
| Retail | Approx. $3 million | High volume of personal data (PII) and PCI-DSS non-compliance fines |
| United States | $9.48 million | A complex web of state laws and significant litigation risk |
| Global Average | $4.44 million | The general benchmark across all sectors and regions combined |
Looking at the numbers this way, it is clear that a "one-size-fits-all" view of breach costs is dangerously misleading. To make informed decisions about security investments, leaders must evaluate their financial risk through the specific lens of their own operating environment.
Tallying Up the Risk: How to Calculate Your Potential Breach Costs and Security ROI
Industry averages provide a useful starting point, but the real work begins when you translate those broad numbers into a specific risk profile for your organization. This is about building a financial model that turns a vague threat into a tangible business risk.
Once you have that number, you can reframe cybersecurity spending. It stops being a line-item expense and becomes a strategic investment with a clear, defensible return.
This process helps you answer the inevitable question from the board: "What is the actual financial risk we are facing here?"
A Simple Model to Get Started
You do not need a complex algorithm to get a baseline estimate. A straightforward calculation based on the number of sensitive records you manage can provide a powerful starting point for executive-level conversations.
The formula is:
Potential Breach Cost = (Number of Sensitive Records) x (Per-Record Cost)
The key is to use a per-record cost that reflects your reality. A U.S.-based healthcare organization, for example, might start with the U.S. average of $264 per record. A retail company in Europe would likely use a lower figure based on regional data.
To make your estimate more accurate, consider a few variables:
- Type of Data: The more sensitive the information (health records, financial data), the higher your per-record cost will be.
- Regulatory Pressure: If you operate under strict regulations like GDPR or HIPAA, potential fines and mandatory notification costs will inflate the number significantly.
- Response Readiness: An organization with a tested incident response plan will almost always have lower total costs than one scrambling to figure things out after an attack.
From Expense to Investment: Proving Security ROI
With a potential cost estimate in hand, you can now calculate the Return on Investment (ROI) for any new security tool or initiative. This shifts the conversation from "How much does this cost?" to "How much will this save us?" It is a language every executive understands.
The formula is simple:
Security ROI = [(Potential Breach Cost x Risk Reduction %) - Cost of Solution] / Cost of Solution
The Risk Reduction % is an estimate of how much a new tool or process will lower the probability or impact of a breach. You can get this figure from vendor data, industry benchmarks, or your own internal risk assessments. Presenting your case this way frames security as a smart financial decision.
The goal is to move cybersecurity from a cost center to a value driver. When you can show that a $500,000 investment in an AI-powered monitoring platform can prevent a potential $5 million loss, the decision becomes a matter of good business sense.
A Synthetic Example: Putting the ROI Formula to Work
Let's walk through a synthetic scenario to see how this plays out.
The Company: A mid-sized U.S. financial firm managing 100,000 sensitive client records.
1. Calculate the Potential Damage The firm uses the U.S. average per-record cost of $264.
- Potential Breach Cost: 100,000 records x $264/record = $26.4 million
2. Evaluate the Proposed Solution The CISO wants to implement an AI-driven security monitoring platform. The annual cost is $400,000.
- Based on performance data for similar technologies, the CISO estimates this platform can reduce the risk of a major breach by 25%.
3. Calculate the Security ROI
- Potential Savings: $26,400,000 x 0.25 = $6,600,000
- ROI: ($6,600,000 - $400,000) / $400,000 = 15.5
The result is a return of $15.50 in avoided breach costs for every dollar spent on the AI solution.
To get a clearer picture of where your organization stands and identify the most impactful opportunities, a structured AI assessment can provide the necessary data. This data-driven approach turns a technical security decision into an undeniable business advantage.
Proven Strategies to Reduce Data Breach Costs
Knowing the financial risks of a data breach is one thing; taking action is another. The goal is to move from awareness to action, which requires a deliberate strategy combining solid processes, skilled people, and the right technology. The most effective investments not only lower the probability of a breach but also cushion the financial impact if one occurs.
Organizations that prepare for incidents consistently experience lower costs. Having a tested Incident Response (IR) plan can reduce the total cost of a data breach by an average of $1.49 million. This is one of the most effective cost-control measures available.
Fortify Processes with Proven Frameworks
Strong processes are the foundation of a resilient security program. Without clear, repeatable procedures, even the best technology and the most talented team can fail under the pressure of a real attack. This is where established security frameworks prove their worth.
Implementing recognized standards is a reliable way to reduce the financial impact of a breach. For example, understanding the ISO 27001 certification benefits shows how a structured approach to managing information security builds validated, stronger defenses.
Here are a few key process-oriented strategies that are effective:
- Incident Response (IR) Planning: Do not just write an IR plan—test it regularly. When everyone knows their role and communication lines are clear, containment actions can be executed swiftly, minimizing chaos and financial loss.
- Regular Security Audits: The best time to find a vulnerability is before an attacker does. Consistent audits and penetration tests expose weaknesses in your infrastructure and processes, allowing you to fix them on your own terms.
- Employee Training Programs: Human error remains a leading cause of breaches. Ongoing training on phishing, social engineering, and proper data handling is essential. An informed workforce is your first line of defense.
A tested Incident Response plan acts like muscle memory for your organization. When a crisis hits, you do not waste precious time and money figuring out what to do—you execute a plan that has been rehearsed and refined.
Accelerate Containment with Security AI
While processes are the foundation, technology is the force multiplier, especially when racing to contain a threat. The faster you can detect and neutralize an attack, the lower your final bill will be. This is where modern, AI-powered security platforms provide a decisive edge.
The average data breach lifecycle can shrink from 277 days to under 100 days when organizations make extensive use of security AI and automation. That acceleration translates directly into cost savings by limiting the scope of the damage.
An AI-driven system does not just react to known threats. It actively hunts for anomalies and suspicious patterns that signal an ongoing attack. It can analyze billions of data points in real-time—a task that is impossible for human teams alone.
Let’s walk through a synthetic example.
An attacker compromises a user account at 2:00 AM on a Tuesday. A traditional security team might not notice the unusual activity until the next morning, giving the intruder hours to access the network and exfiltrate data. An AI monitoring system, in contrast, flags the anomalous login instantly, isolates the compromised account, and alerts the security team within minutes. The breach is stopped before it can fully develop. This swift action turns a potential multi-million dollar disaster into a contained, low-impact security event.
Building a Business Case for Modern Security
The link between advanced technology and lower breach costs is direct and quantifiable. By reducing the time from detection to containment, AI-powered security delivers a clear and compelling return on investment.
- Faster Threat Detection: AI algorithms spot subtle indicators of compromise that often go unnoticed by traditional, rule-based systems.
- Automated Containment: Once a threat is verified, automated workflows can quarantine affected systems, block malicious traffic, and disable compromised accounts in seconds.
- Reduced Analyst Fatigue: By handling the initial volume of alerts and analysis, AI frees up human experts to focus on complex, high-stakes investigations.
Organizations looking to put real numbers behind these benefits should start with a detailed security posture evaluation. Getting a clear view of your current defenses with a comprehensive data security and AI audit can pinpoint exactly where automation and intelligent monitoring will deliver the biggest cost reductions, giving you the information needed to build a powerful business case for strategic investment.
A Practical Checklist for Executive Breach Preparedness
Knowing the risks is one thing; acting on them is what matters in managing the fallout from a data breach. For C-suite leaders and board members, the key is asking the right questions—not to conduct a technical audit, but to spark essential strategic conversations with your security team.
Think of this checklist as a tool to bridge the gap between your security posture, business goals, and tolerance for financial risk.

Financial and Risk Alignment
First, ensure the security strategy is connected to its financial impact. A disconnect here can lead to underfunded programs and significant financial surprises when an incident occurs.
- Financial Risk Quantification: Have we quantified the potential cost of a data breach for our specific business? This should be based on our data assets, industry, and geography—not just generic statistics.
- Insurance Coverage Review: Does our cyber insurance policy adequately cover the financial risks we have identified? Review the fine print for coverage of regulatory fines and legal fees.
- Third-Party Risk Assessment: Have we vetted the security of our critical suppliers and partners? Our guide to Third-Party Risk Management (TPRM) provides a solid framework for this.
Operational Readiness and Response
Next, consider your team's ability to perform under pressure. A slow or chaotic response multiplies both financial cost and brand damage.
A well-rehearsed incident response plan is the single most effective tool for cost containment. It transforms chaotic reaction into disciplined execution, saving millions in the process.
- Incident Response Plan: Do we have a documented IR plan? More importantly, have we tested it with a realistic drill in the last six months?
- Containment Speed: What is our current "time to contain" a threat, and what is our concrete goal for reducing that number?
Technology and Modernization
Finally, ensure your technology is a strategic asset. The right tools can dramatically reduce both the probability of a breach and its severity.
- Automation and AI: Are we using security AI and automation to find and stop threats faster? This is a direct lever for lowering containment costs.
- Data Visibility: Do we have a complete and updated map of where our most sensitive data resides, whether on-premises or in the cloud? You cannot protect what you cannot see.
Frequently Asked Questions
Even after calculating the obvious expenses, leaders often have questions about the less visible financial fallout of a data breach. Clarifying these issues is crucial for building a complete picture of your company's risk.
What Are the Biggest Hidden Costs of a Data Breach?
The costs on the initial incident response invoice are only the beginning. Several "long-tail" costs can impact your company's resources for years and are often missed in the initial damage assessment.
Here are a few of the most damaging ones:
- Increased Insurance Premiums: After an incident, your cybersecurity insurance provider will view you as a higher risk. Expect annual premiums to increase significantly at renewal.
- Eroded Brand Trust: This is difficult to quantify but can be devastating. A breach damages your reputation, leading to customer churn and making it harder to win new business. The revenue impact can last for years.
- A Higher Cost of Capital: A major breach can concern investors and credit agencies, potentially leading to a credit rating downgrade. Borrowing money for future growth initiatives can become more expensive.
How Long Does the Financial Impact of a Breach Last?
The financial impact of a data breach does not end once the security team has contained the threat. A significant portion of the total cost materializes long after the attack has been neutralized.
Research from IBM shows that while 52% of breach costs are incurred in the first year, 31% emerge in the second year, and 17% can appear more than two years later. This long financial tail is usually a combination of legal battles, regulatory penalties, and the slow loss of customers.
Does Paying a Ransom Reduce the Cost of an Attack?
It may seem that paying a ransom is the fastest way out of a ransomware attack, but the data suggests otherwise. In reality, it often backfires and leads to higher total costs.
There is no guarantee that the attackers will return your data or provide a working decryption key. Paying a ransom also marks your company as a target for other criminal groups.
Even if you recover your data, you still face the expense of rebuilding your systems to ensure the attackers' malware is completely removed. You may end up paying twice: once for the ransom and again for the full-scale recovery effort. It is almost always a losing financial strategy.
Ready to turn your data into a secure, competitive advantage? DSG.AI designs, builds, and deploys production-grade AI solutions that deliver measurable value. See how we've helped global leaders optimize operations and strengthen their security posture. Explore our successful AI projects.