Written by:
Editorial Team
DSG.AI
Organizations need to extract insights from sensitive information without compromising individual privacy. This is a central challenge for modern data and AI initiatives. Privacy-Enhancing Technologies (PETs) provide a technical framework to connect the need for data analysis with the right to privacy.
Why Data Privacy Is a Business Imperative
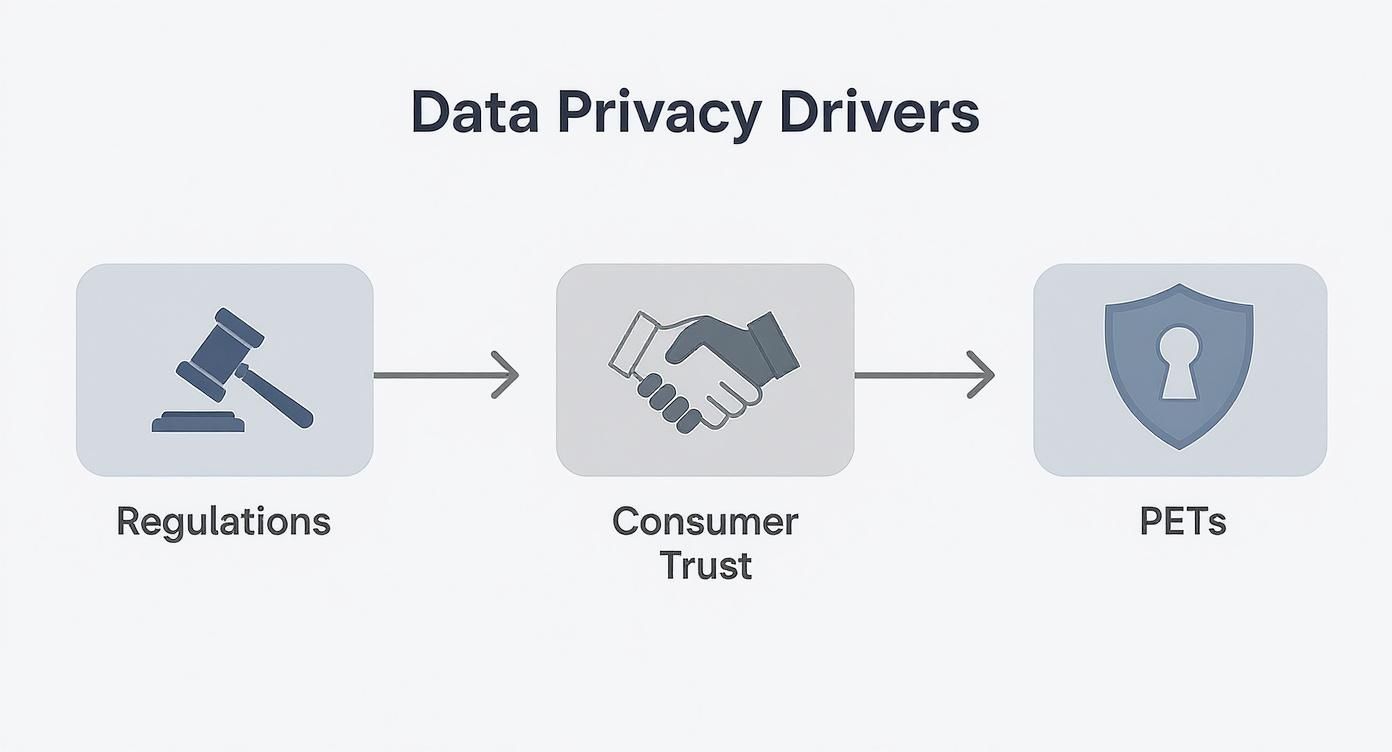
Pressure to manage data protection has intensified. This is driven by two forces: regulations with financial penalties and consumers who are more aware of their data rights. Failure to meet these expectations can lead to fines, operational disruption, and erosion of customer trust.
Traditional security measures like firewalls and access controls protect data at rest. They do not, however, protect data while it is being analyzed or processed. PETs are designed to fill this specific gap.
The Market Is Investing in Privacy
Organizations are shifting from reactive privacy fixes to proactive, privacy-by-design operations. The global PETs market, valued at approximately USD 3.1 billion, is projected to reach USD 12.1 billion by 2030. This represents a compound annual growth rate (CAGR) of 25.3% from 2025 to 2030. This growth indicates a fundamental change in data strategy. For detailed figures, see the full PETs market report.
This growth is based on three key factors:
- Complex Regulations: Rules like GDPR and the EU AI Act mandate data minimization, purpose limitation, and secure processing.
- Consumer Expectations: A 2023 consumer survey showed that 81% of respondents view a company's data handling as a reflection of how it values them as a customer.
- Secure Collaboration: Businesses must collaborate on shared challenges, such as fraud detection or medical research. PETs enable this collaboration without exposing raw, sensitive data.
For a CTO or Head of Data, PETs are a tool for innovation, not just compliance. These technologies enable work with sensitive datasets that were previously inaccessible, creating a competitive advantage based on trust.
Understanding Core Privacy Enhancing Technologies
Each core PET provides a different method for protecting data during its use. Understanding these mechanisms is the first step toward building a data strategy that prioritizes privacy.
The adoption of these technologies is a direct response to market forces. Evolving regulations require greater consumer trust, which in turn makes PETs a business necessity.
PETs are a technical solution to specific business and regulatory requirements.
Homomorphic Encryption: Working with Encrypted Data
Homomorphic encryption allows for computations on encrypted data without first decrypting it. The result of the calculation remains encrypted. Only a party with the correct key can decrypt the final output. This is a powerful method for outsourcing data processing to third-party environments, like a cloud service.
Synthetic Example: A financial firm sends encrypted transaction data to a cloud provider for analysis. The cloud provider performs calculations on the encrypted data and returns an encrypted result. The analyst gets insights, and the cloud provider performs the computation, but neither party sees the raw, unencrypted information.
Differential Privacy: Hiding Individuals in a Dataset
Differential privacy adds a small amount of statistical noise to a dataset. When a query is run—for example, "What is the average age?"—the added noise makes it mathematically impossible to determine if any specific individual was part of the original data.
The technique introduces calibrated statistical noise into query results. This noise is sufficient to protect individual identities but does not significantly distort aggregate trends. This is useful for public data releases or internal analytics where protecting individual privacy is required. A city could release transit usage data without revealing any single person's travel habits.
Secure Multi-Party Computation: Collaborative Analysis Without Data Sharing
Secure Multi-Party Computation (MPC) allows multiple parties to jointly compute a result from their private data without revealing that data to each other.
Synthetic Example: Several competing banks want to identify a fraudulent actor they all suspect is targeting their systems. None can share their confidential transaction lists. Using MPC, each bank inputs its encrypted data into a shared calculation. The system outputs only the final result—a list of suspicious accounts common to all participants. Each bank's private dataset remains hidden from the others. This enables collaboration in finance, healthcare, and intelligence.
Comparing Key Privacy Enhancing Technologies
The following table compares the functions and common applications of core PETs. Each technology offers a different balance of privacy and utility.
| Technology | Primary Function | Best Use Case | Key Trade-off |
|---|---|---|---|
| Homomorphic Encryption | Performing computations on encrypted data. | Outsourcing sensitive data processing to untrusted cloud environments. | High computational overhead can impact performance. |
| Differential Privacy | Adding statistical noise to query results to protect individuals. | Sharing aggregate data publicly or for internal analytics without re-identification risk. | A direct trade-off between privacy level (more noise) and data accuracy. |
| Secure MPC | Jointly computing a result from multiple private inputs. | Collaborative data analysis between parties who cannot share raw data (e.g., fraud detection). | Requires significant communication and coordination between parties. |
| Federated Learning | Training ML models on decentralized data sources. | Training models on user data that cannot leave the device (e.g., mobile phones). | Model updates, not raw data, can still potentially leak some information. |
| Secure Enclaves (TEE) | Creating isolated, hardware-protected processing environments. | Protecting data and code in use, even from the host system administrator. | Dependent on specific hardware; potential for side-channel attacks. |
| Synthetic Data | Generating artificial data that mimics a real dataset's properties. | Safely sharing data for software testing, analytics, or AI model training. | The generated data may not capture all the nuances of the original dataset. |
There is no single "best" PET. The correct choice depends on the specific problem.
Additional Key PETs
Other technologies are also part of the PET toolkit:
- Federated Learning: Instead of moving data to a central server, this technique sends the machine learning model to where the data resides. The model trains locally, and only updated model parameters—not the raw data—are sent back.
- Secure Enclaves (Trusted Execution Environments): These are secure vaults built into a processor. They create an isolated, hardware-based space where code and data are shielded from the rest of the system, including the host operating system.
- Synthetic Data: This is the process of creating an artificial dataset that mirrors the statistical properties of a real, sensitive one. Since it contains no actual personal information, it can be used for software testing, model training, and product demos without privacy risk.
Understanding methods like end-to-end encryption (E2EE) is also important for securing data in transit. While all PET categories are growing, cryptographic techniques lead the market. The global PETs market, valued at $2.7 billion, is projected to reach $18.9 billion by 2032, expanding at a CAGR of nearly 26.9%.
The Trade-off: Balancing Privacy and Data Utility
Adopting PETs requires managing a fundamental trade-off. Stronger privacy protections often reduce the utility of the data for analysis. The key is to find the optimal point on this spectrum for a given project.
This trade-off is visible in specific technologies. For Differential Privacy, increasing privacy requires adding more statistical noise. This noise protects individuals but can also reduce the accuracy of machine learning models. Depending on the dataset, this accuracy reduction can range from 5 to 10 percent.
Homomorphic Encryption allows calculations on encrypted data but comes with a significant performance cost. Computations that take seconds on unencrypted data can take minutes or hours. This makes it unsuitable for real-time applications but practical for sensitive, offline batch processing where latency is not a primary constraint.
Finding the Right Balance
Every PET operates on a spectrum between perfect privacy and maximum data utility. Your objective is to determine where your project needs to be on this spectrum to meet business goals without introducing unacceptable risk or performance degradation.
Synthetic Example: A public health agency releasing population statistics can accept lower data granularity to ensure anonymity. In contrast, a bank training a fraud detection algorithm requires high accuracy and may need to accept a slightly lower privacy guarantee to ensure the model is effective.
Before selecting a technology, you must define the minimum acceptable accuracy and the maximum tolerable privacy risk for your use case.
Beyond the Performance Trade-off
Other practical challenges can impact a project's timeline and budget.
- Integration Complexity: PETs must be integrated into existing data pipelines, analytics tools, and ML workflows. This often requires new architectural patterns, such as a dedicated "Privacy Gateway" to treat data before it reaches an analyst.
- Specialized Skills: The talent pool for professionals with practical experience in applied cryptography or differential privacy is limited.
- Governance and Monitoring: Deployed PETs require constant oversight. This includes policies defining who can access protected data, what they can do with it, and how to monitor for potential privacy breaches.
A structured plan is necessary to navigate these challenges. An AI readiness assessment can identify gaps in infrastructure, team skills, and governance policies before a large-scale investment is made.
Integrating PETs into Your Enterprise Architecture
Moving PETs from concept to production requires a clear architectural plan. These technologies are not plug-and-play. They must be integrated into an existing data stack to provide value. The goal is to build privacy into systems by design.
Two common architectural patterns are the Privacy Gateway and the Federated Analytics model. Each offers a different approach for handling sensitive data.
The Privacy Gateway Pattern
A Privacy Gateway is a centralized service that acts as a mandatory checkpoint for sensitive data. Before raw information enters a data lake or analytics environment, it passes through this gateway.
The gateway's function is to apply a PET, like differential privacy or data synthesis, to de-identify the data stream. This creates a separation of concerns:
- Upstream Systems: Data ingestion pipelines continue to collect raw information as before.
- Downstream Systems: Analytics platforms, ML training environments, and data scientists only work with the privacy-preserved version of the data.
This approach reduces the risk of accidental exposure by confining raw, sensitive data to a small, controlled part of the architecture.
The diagram below illustrates this model, with data sources filtered through a central privacy layer.

This pattern makes privacy a managed service within the infrastructure, simplifying governance and compliance.
The Federated Analytics Model
The Federated Analytics model reverses the traditional data processing flow. Instead of bringing data to the model, the model is brought to the data. This is effective when data is decentralized and cannot be moved due to regulations or volume, such as user data on mobile devices or patient records across different hospitals.
A central server coordinates the training process without accessing the raw data.
- A global machine learning model is distributed to each data source (node).
- The model trains on the local data at that specific location.
- Only the model updates—the learned parameters, not the data—are sent back to the central server.
- The server aggregates these updates to improve the global model, which is then redistributed for the next training round.
This method ensures that sensitive information never leaves its secure, local environment. A recent pilot project between the NHS and the US National Cancer Institute used a federated approach, reducing a governance process that typically takes over a year to just two months.
This model enables the development of collaborative AI models without centralizing or directly accessing the sensitive datasets they rely on.
Connecting PETs to AI and ML Pipelines
Integrating these patterns into an MLOps framework requires careful planning. A Privacy Gateway can become a standard pre-processing step, automatically feeding anonymized data into model development environments. Implementing these workflows requires an understanding of modern data and AI orchestration.
A federated learning setup requires a robust infrastructure to manage model distribution, versioning, and secure aggregation. The choice between these patterns depends on the use case, data location, and compliance obligations.
Meeting Modern Compliance Frameworks with PETs
Privacy-enhancing technologies are a core component for navigating modern regulations. Integrating PETs is a strategic approach to manage risk, justify technology investment, and build trust with customers and regulators.
This has created a significant market opportunity. The privacy-enhancing technology market is projected to reach USD 40.0 billion by 2035, up from USD 3.8 billion in 2025. This growth is driven by increasing regulatory focus on data protection. You can explore the growth drivers in the PET market.
This trend signals a change in compliance strategy. It is no longer sufficient to have policies on paper. Regulators now require proof that privacy is integrated into systems by design.
Aligning PETs with Key Regulations
Different PETs map directly to specific principles in major data protection laws. Frameworks like the GDPR compliance requirements are mandatory. PETs provide the technical means to meet these legal obligations.
Consider two of GDPR’s core principles: 'data minimization' and 'purpose limitation.' These require organizations to collect only necessary data and use it only for its stated purpose.
-
Synthetic Data supports data minimization. It allows teams to generate artificial datasets that mimic real data. They can build, test, and demo products without exposing actual customer data.
-
Differential Privacy is a tool for purpose limitation. It allows data scientists to extract aggregate insights from a dataset while making it mathematically impossible to re-identify any individual.
Connecting a specific technology to a specific legal requirement provides a clear business case for its adoption.
Proving Compliance for Advanced AI Systems
As regulations like the EU AI Act are implemented, the role of PETs will become more central. These laws require a higher standard of data governance, fairness, and security, particularly for training and deploying AI models.
Secure Enclaves are a direct response to mandates for secure data processing. They create a hardware-isolated environment for data. An AI model can be trained on sensitive information inside the enclave, ensuring the data is never exposed. This provides a verifiable audit trail.
This type of technical proof is what regulators expect to see. An EU AI Act readiness assessment can help identify gaps and plan a path forward. Integrating PETs is a foundational step for building a resilient AI strategy.
Creating Your PETs Implementation Roadmap
A successful rollout of Privacy-Enhancing Technologies is a phased process that builds momentum, proves value, and manages risk. Breaking the process into three stages—Assessment, Pilot, and Scaling—provides a practical path from concept to enterprise capability.

Phase 1: The Assessment
The first step is to identify the right starting point. The goal is to find a use case with high business impact and relatively low technical complexity. An internal analytics project is often a good candidate.
Synthetic Example: An HR department wants to analyze employee performance and retention data but is blocked by the sensitive nature of the information. This is a contained scenario to demonstrate the value of PETs.
During this phase, your team should:
- Identify 3-5 potential use cases by consulting with business units.
- Score each use case based on business value, data sensitivity, and implementation difficulty.
- Select a single initial project that offers the best balance of impact and feasibility.
Phase 2: The Pilot Program
With a use case selected, the next step is a focused pilot program. The objective is to test the technology, define success metrics, and choose a vendor or solution. It is critical to set clear and measurable goals.
Instead of a vague goal like "improve privacy," define a specific metric. For example: "Maintain model accuracy within a 5% margin of the non-private baseline while satisfying the data anonymization standard."
A quantitative target provides the technical team with a clear objective and gives leadership a tangible measure of the pilot's success. This is also the stage for vetting potential technology partners.
A vendor evaluation should assess:
- Technical Performance: How does the solution handle your data volumes and query complexity?
- Ease of Integration: How well does it integrate with your existing data stack (e.g., Snowflake or Databricks) and ML frameworks?
- Governance and Auditability: What tools are provided for monitoring access, enforcing policies, and generating compliance reports?
- Support and Expertise: Does the vendor provide domain expertise to help with implementation?
Phase 3: Scaled Implementation and Governance
After a successful pilot, the project can move to a broader rollout. This phase focuses on establishing the operational framework to manage PETs at scale. This involves creating governance policies and monitoring systems.
Your governance framework should define:
- Access Control: Who can request access to privacy-preserved data and for what purpose?
- Usage Policies: What types of queries or analyses are permitted on specific datasets?
- Monitoring Procedures: How will you track system performance and audit data usage to ensure compliance?
This structured approach helps turn PETs from an abstract concept into a managed, scalable capability.
Real-World Implementation Examples
-
A Financial Services Consortium: A group of banks needs to collaborate to detect a fraud ring operating across their institutions. They cannot share raw customer data. They use Secure Multi-Party Computation (MPC) to jointly analyze transaction patterns. Each bank contributes encrypted data, and the system outputs a shared list of high-risk accounts. Client confidentiality is maintained while collective security is enhanced.
-
A Healthcare Research Network: A network of hospitals wants to train an AI model to identify early signs of patient deterioration. Centralizing this sensitive data is not feasible due to regulations. The solution is Federated Learning. The AI model is trained locally within each hospital's secure environment. Only anonymized model updates are sent back to a central server, building a predictive tool without patient records ever leaving the hospital.
Answering Your Questions About PETs
Integrating a new class of technology raises common questions from business leaders.
Do PETs Replace Our Existing Security?
No. PETs work with, not against, existing security measures.
Traditional security—firewalls, access controls, and data-at-rest encryption—protects the container. PETs protect the data while it is being used. They protect the privacy of individuals represented in the data, even during active analysis. Both are necessary.
How Do We Justify the Investment? What's the ROI?
The return on investment for PETs includes both quantitative and qualitative factors.
Quantitative gains include:
- Revenue from new data collaborations or products that were previously blocked by privacy restrictions.
- Faster, more efficient data analysis due to the removal of internal privacy hurdles.
- The avoided cost of compliance fines or brand damage from a data incident.
The qualitative ROI comes from building a reputation as a trustworthy brand, which can increase customer loyalty and provide an advantage in partnership negotiations. This turns a commitment to privacy into a competitive advantage.
We Are Convinced. Where Do We Begin?
Start with a small, focused project. Do not attempt a large, company-wide rollout initially. Select a single, high-impact project to demonstrate value quickly.
A good starting point is often an internal project, like running analytics on sensitive HR data. Another option is a research project with a partner where insights must be combined without sharing raw data. Training a machine learning model on regulated information is also a common starting point.
This "quick win" approach allows your team to learn in a controlled environment, demonstrate business value, and build momentum for broader adoption.
DSG.AI designs and builds enterprise-grade AI solutions with privacy at their core. We provide architectural guidance and engineering to integrate PETs into your data stack. Explore our enterprise AI projects to see how we deliver measurable business value.